
Graphic Hub Administrator Guide
Version 3.8 | Published February 06, 2023 ©
SSL in REST
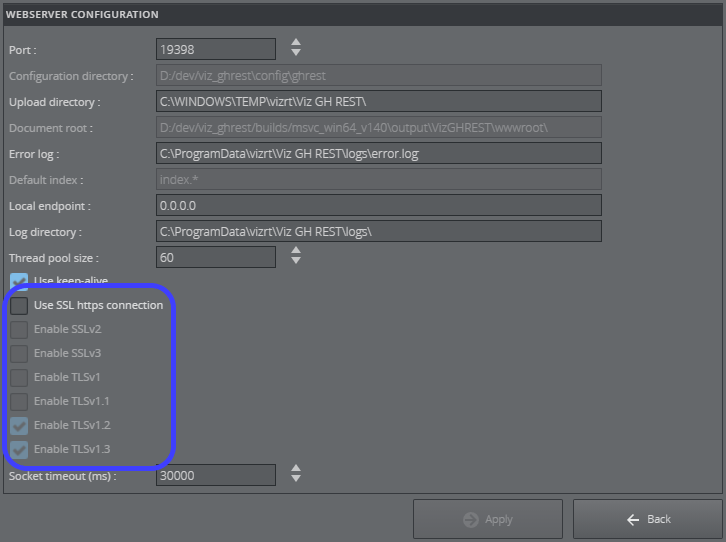
SSL/TLS can be activated in GH REST by enabling Use SSL HTTPS connection in Web Server Configuration Settings. This encrypts connections to the REST interface using the HTTPS protocol. If the HTTPS page includes content retrieved through a regular HTTP connection, the connection is only partially encrypted. Most popular browsers block mixed content by default.
Information: The certificate, private key and password can be changed by modifying the current GH REST installation.
In the Web Server Configuration panel the SSL/TLS versions, to be supported by the server, can be chosen from the option list once the Use SSL https connection option is enabled.
SSL/TLS Configuration
To configure GH REST to support HTTPS (HTTP over SSL/TLS) connections the following information is needed:
-
Certificate, Private Key and Password.
-
Vizrt Viz GH REST SSL/TLS Configuration.
-
Verification of New SSL/TLS Configuration.
Certificate, Private Key and Password
The certificate and private key files must be .pem filetype. The generation of those files is in the responsibility of the customer.
OpenSSL for Windows (Optional)
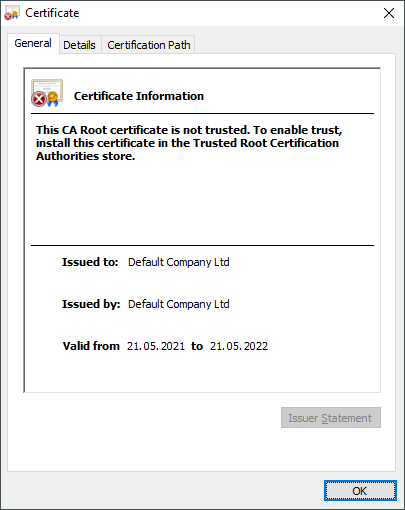
IMPORTANT! Self-signed certificates are highly discouraged for production because they are meant for testing purposes only.
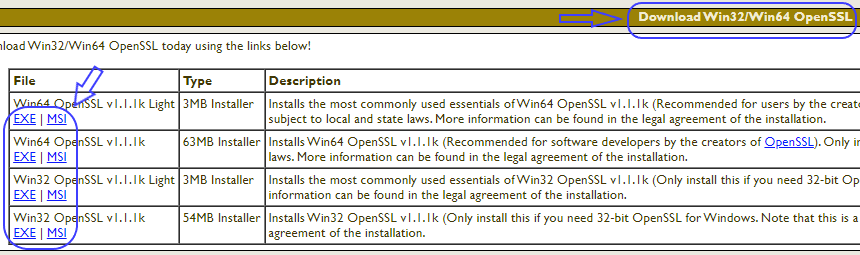
Optionally, for testing purposes, OpenSSL for Windows can be utilized to create a self-signed Certificate Signing Request (CSR) which generates the certificate and private key files.
-
OpenSSL for Windows can be downloaded and installed from https://slproweb.com/products/Win32OpenSSL.html:
-
Using the command line the installation of OpenSSL can be verified using:
openssl version
-
A self-signed CSR, combined with a password (which should not be forgotten), can be generated using:
openssl req -x509 -newkey rsa:4096 -keyout server_key.pem -out server_cert.pem -days 365
The newkey option can also be rsa:2048.
-
The file pair, of certificate and private key, can be found in the directory where the above command was executed:
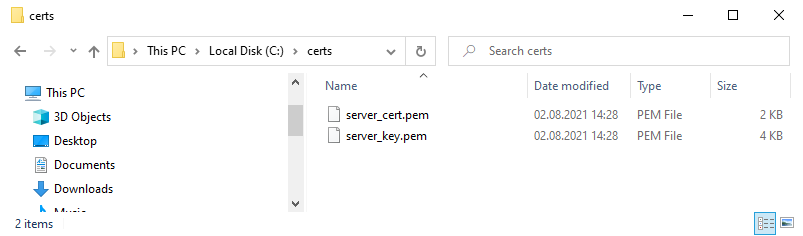
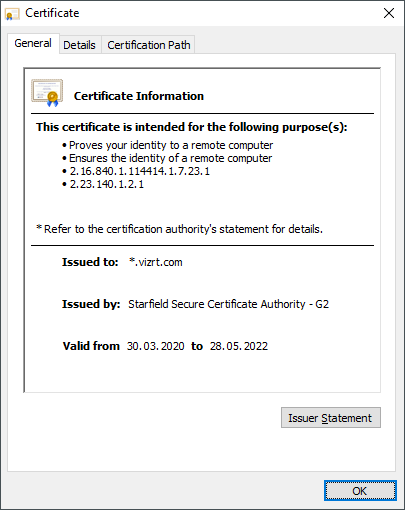
How Graphic Hub REST looks in a browser with a self-signed certificate (left) compared to vizrt.com (right):
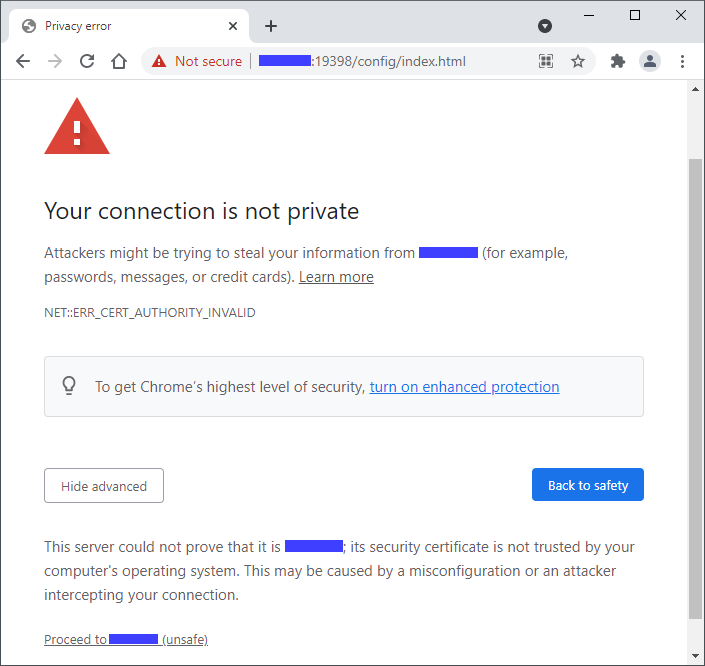
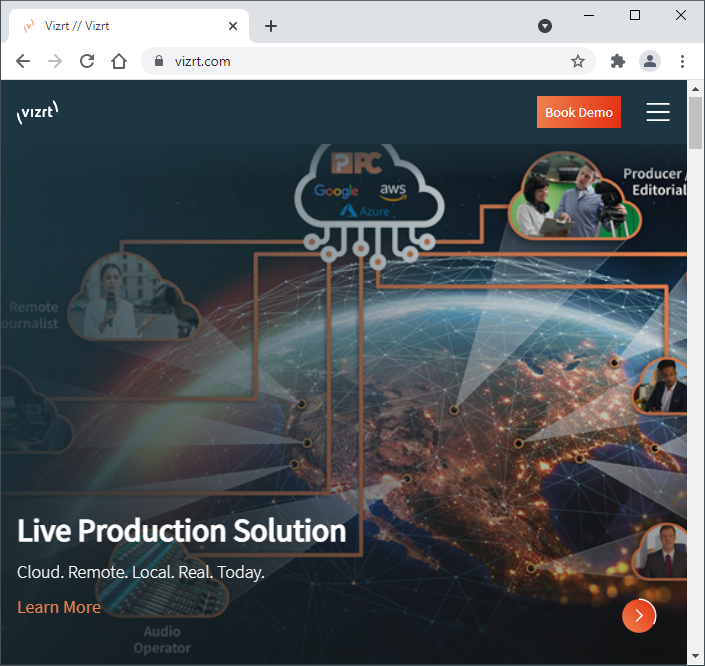
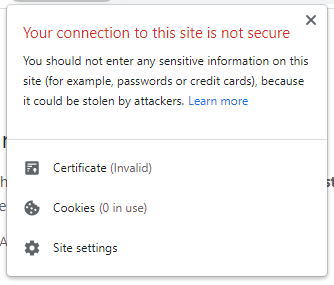
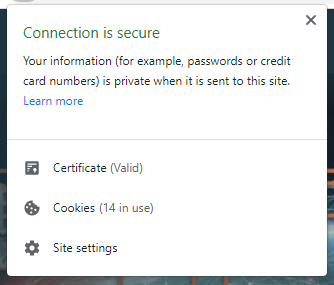
An invalid self-signed certificate indication (left) compared to a valid one (right).
Vizrt Viz GH REST SSL/TLS Configuration
-
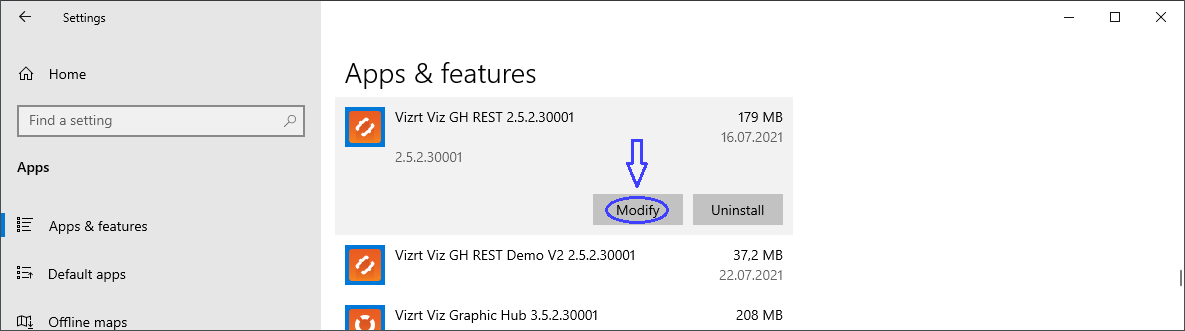
The certificate, private key and password can be changed in GH REST by modifying the installation:
-
In modern Windows versions, Settings > Apps > Vizrt Viz GH REST > Modify can be used.
-
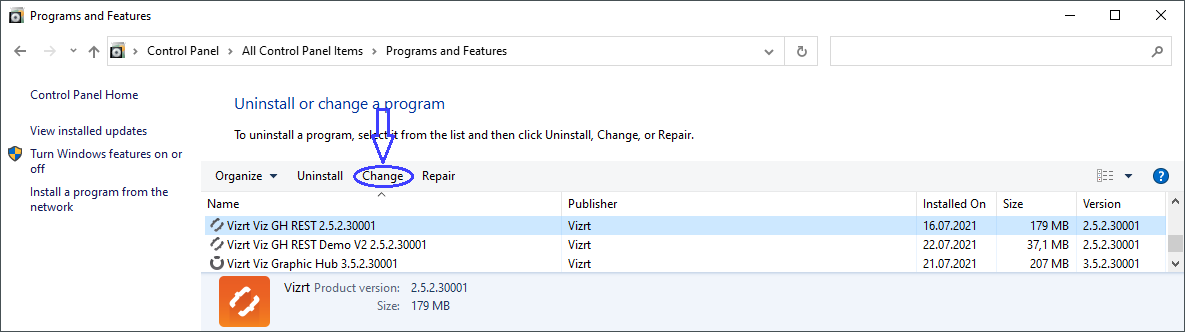
In older Windows versions, Control Panel > Programs and Features > Vizrt Viz GH REST > Change can be used.
-
-
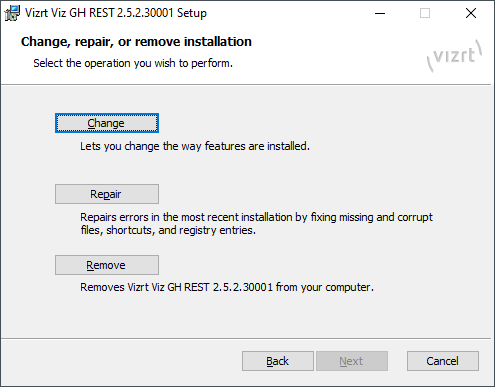
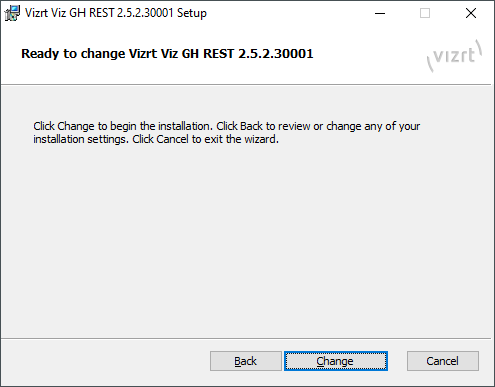
In the Change, repair or remove installation phase click Change:
-
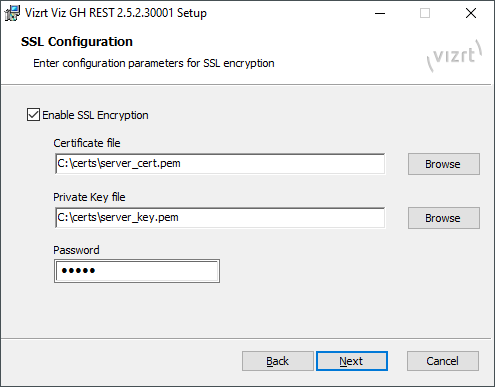
Click Next a few times to navigate the installation wizard to the SSL Configuration phase and place the file paths and password in the fields:
Important: Files with limited accessibility (unprivileged or from network shares) may cause access issues in GH REST where the installer is unable to complete or start the server.
-
Click Next a few times and then click Change:
-
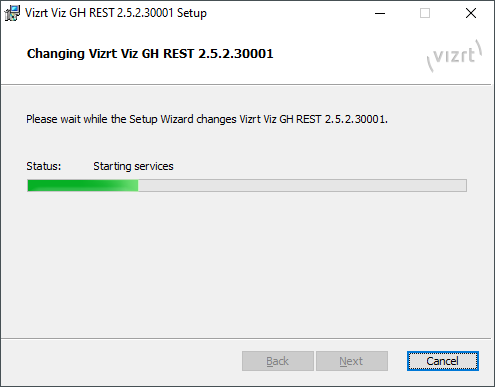
When the installer completes click Next, then Finish:
Verification of New SSL/TLS Configuration
-
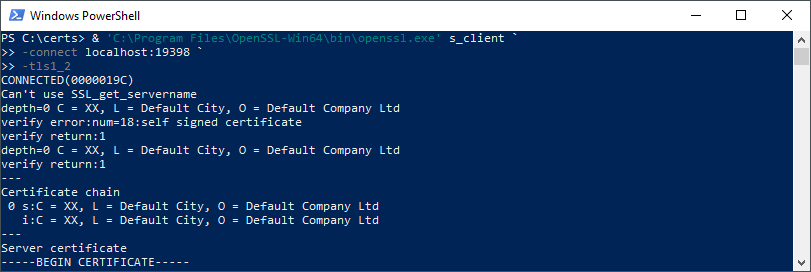
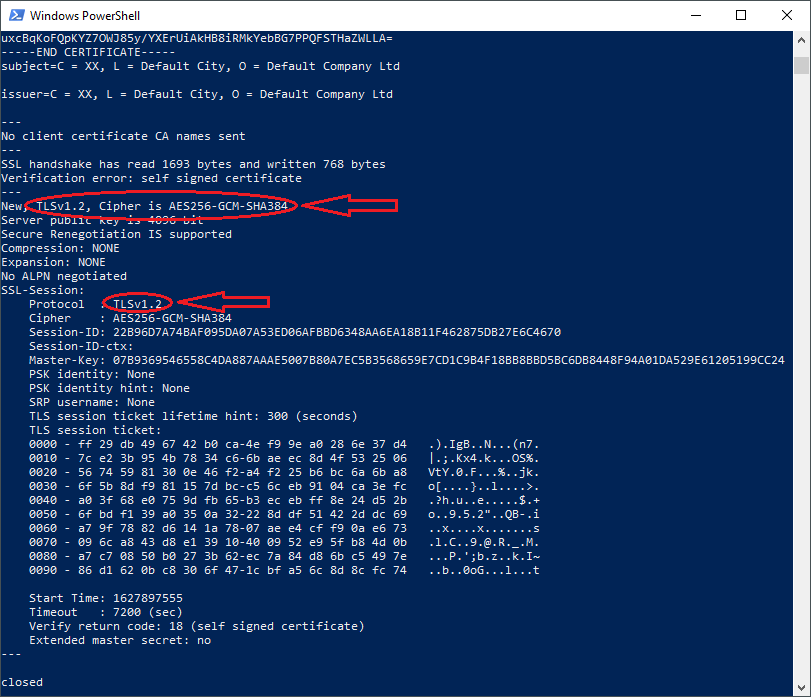
The status of the new configuration can be tested using OpenSSL (for example, to test TLSv1.2):
openssl s_client -connect localhost:19398 -tls1_2
-
As a verification, the specified protocol in the command is displayed in the output under SSL-Session > Protocol:
GH Terminal
While the Graphic Hub REST interface can run with SSL/TLS encryption, Graphic Hub Terminal cannot. Because of this, the connection between them is considered mixed content and hence blocked. This may cause an Unable to connect error message:
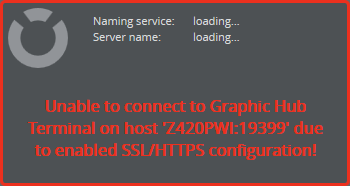
This is not an issue and can be ignored, as it is just a status display in the Web UI. If desired, it can be resolved by adding a security exemption, which is not recommended. The steps to do this depend on the browser in use:
-
Google Chrome
-
Click the shield icon in the right of the address bar, or
-
Start Chrome from the command line using the additional flag --allow-running-insecure-content.
-
-
Internet Explorer
-
Scroll to the bottom of the screen and click Show all content.
-
-
Mozilla Firefox
-
Click the shield icon to the left of the address bar.
-
Click the arrow next to the Connection is Not Secure warning, and select Disable protection for now.
For details on how to show mixed content in other browsers, please refer to the documentation for the browser in question.
-